SaaS Tenant: Building or Reusing Available SaaS Framework for Your Product
An emerging software delivery model, ‘SaaSTenant™ 2.1’ (Software as a Service) allows developers to leverage their existing .NET assets and […]

Cloud Access Security Broker ensures application security
Taking the cyber crimes lightly can be a dangerous game for enterprises if they ignore the threats related to cyber […]

Idea manifesting your dream-business into reality
When you plan a business, your first concern is investment. Every business aims at profits and Return on Investment (ROI). […]
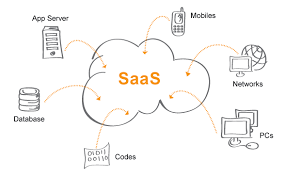
Defusing the Challenges of Tech Companies with Unique Outsourcing Model
In the world of technology, everything gets quickly updated and quickly obsolete. This is beyond devices and platforms and even […]

Necessity of Security Operations Center
Nothing guarantees foolproof cyber security as hackers keep on coming with new ideas to breach the barriers meant for cyber […]

Front End Web & App Development
When the concept of Internet was new, web-development was for the most part a purely functional data centric endeavor. User […]

LTS offers Cyber Security Services to Aviation Firm
Pune, India – May 09, 2017: The cyber security services of LTS are set to fly and counter the penetration […]
Single Sign On ensures foolproof security for passwords and user accounts
In a world where cyber criminals are watching over corporate networks, waiting for opportunity to pounce and steal the corporate […]

Overcoming challenges of Outsourcing
In today’s worldwide world, outsourcing is viewed as a well known method for getting most extreme work at least wages. […]
SaaS Development – Challenges of Transition
Software as a Service (SaaS) has revolutionized the traditional use of software. Software hosted at a central location by a […]