Uniting Athletes Distanced By Geographies With Run2Geo
Work to home, home to work, maybe an occasional pint or two of beers! Aren’t all our stories similar when […]

Digital Marketplace Allowing Maximum Control To Music Artists
While the global music industry is one giant revenue machine, the internal details are not as appealing. When we talk […]

Globally dispersed college teams buddy-up through CAFL

.NET Application Development Company
The expansion of the virtual world has majorly transformed the way business operates and its arena. For present-day, small and […]

Node.js Development Company: Features Of Node.js And Its Business Values
Node.js development is gaining popularity due to real-time applications, fast and scalable solution. It has numerous features which enhance the […]

LTS A Web Development Company In Chicago
Over a decade, LTS a web development company in Chicago is serving in web design and application development projects, possesses […]

Angular JS Application Development For Startup
As per the Google’s report, due to the bad online experience around 40 % of the website users are moved […]
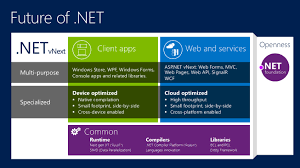
What is the next generation of the .NET ?
If you are thinking about the .NET framework for your next project, there are few upgrades in the platform. The […]

Key Result Area (KRA) Tracking
Introduction : A key result area (KRA) is an strategic factor either internal to the organization or external, where strong […]

Courier Management
Introduction : The main concern of the courier agency is to deliver the right parcel to its owner. To accomplish […]